Cryptographic Key Management: A Practical Guide to Encryption Algorithms, Key Derivation, and Key Rotation
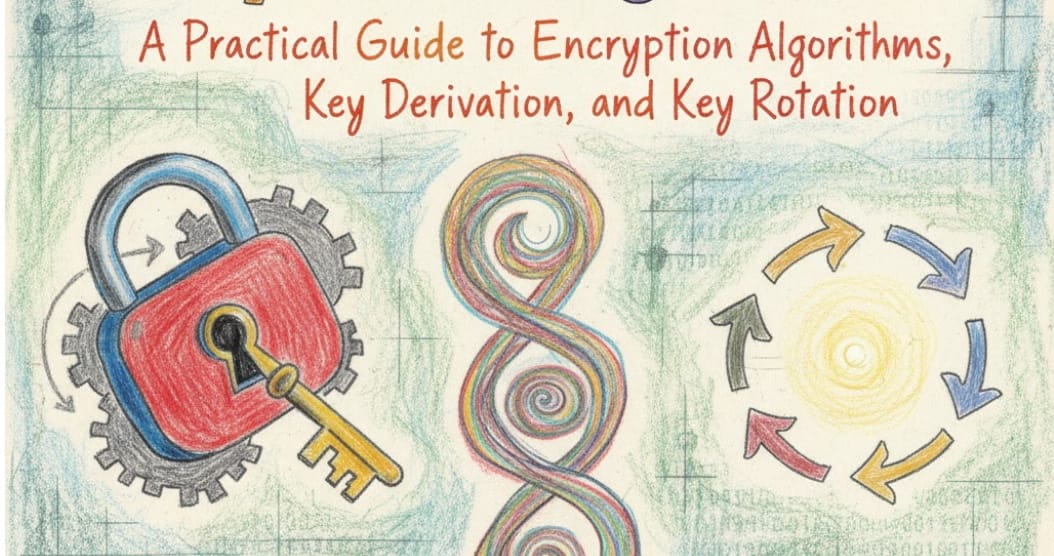
In today's digital landscape, data security isn't optional—it's fundamental. Whether building a fintech platform, healthcare application, or cloud service, understanding cryptographic key management separates robust systems from vulnerable ones. This guide explores the essential pillars of modern cryptography: encryption algorithms, key derivation functions, and key rotation strategies that protect data at scale.
Understanding Modern Encryption Algorithms
Encryption algorithms form the foundation of data security. These mathematical functions transform readable data (plaintext) into unreadable ciphertext, ensuring confidentiality even if attackers intercept the data.
Symmetric Encryption: Speed and Efficiency
Symmetric encryption uses the same key for both encryption and decryption. This approach offers exceptional performance, making it ideal for encrypting large volumes of data.
AES (Advanced Encryption Standard) remains the gold standard for symmetric encryption. Adopted by the U.S. government in 2001, AES operates on 128-bit blocks with key sizes of 128, 192, or 256 bits. Its hardware acceleration support in modern CPUs makes it remarkably fast—capable of encrypting gigabytes per second. Major cloud providers use AES-256 for data at rest, while TLS 1.3 leverages AES-GCM for encrypted web traffic.
ChaCha20 emerged as a modern alternative, particularly for mobile and embedded devices. Designed by Daniel J. Bernstein, this stream cipher excels on platforms lacking AES hardware acceleration. Google adopted ChaCha20-Poly1305 for Android encryption and Chrome's TLS implementation, demonstrating its real-world viability.
The choice between AES and ChaCha20 often depends on hardware capabilities. Systems with AES-NI instructions benefit from AES's superior performance, while devices without dedicated crypto hardware see better results with ChaCha20.
Asymmetric Encryption: Public Key Cryptography
Asymmetric encryption uses paired keys—one public, one private. This elegant solution enables secure communication between parties who've never met, forming the backbone of internet security.
RSA (Rivest-Shamir-Adleman) pioneered public key cryptography in 1977. RSA's security relies on the computational difficulty of factoring large prime numbers. Key sizes of 2048 bits provide adequate security for most applications, though 4096-bit keys offer additional protection for highly sensitive data. RSA excels at key exchange and digital signatures but performs significantly slower than symmetric algorithms.
Elliptic Curve Cryptography (ECC) provides equivalent security to RSA with dramatically smaller key sizes. A 256-bit ECC key offers comparable security to a 3072-bit RSA key, resulting in faster computations and reduced bandwidth. ECDSA (Elliptic Curve Digital Signature Algorithm) handles digital signatures, while ECDH (Elliptic Curve Diffie-Hellman) manages key exchange. Bitcoin, Ethereum, and modern TLS implementations rely heavily on ECC.
In practice, most systems combine both approaches: asymmetric encryption establishes secure channels and exchanges symmetric keys, then symmetric encryption handles bulk data encryption.
Key Derivation: Transforming Passwords into Cryptographic Keys
Passwords present a fundamental challenge—humans create weak, memorable strings while cryptographic systems require high-entropy keys. Key derivation functions (KDFs) bridge this gap by transforming passwords into strong cryptographic keys.
Password-Based Key Derivation
PBKDF2 (Password-Based Key Derivation Function 2) applies a pseudorandom function (typically HMAC-SHA256) thousands of times to a password combined with a salt. This iteration count deliberately slows computation, making brute-force attacks impractical. The salt—a random value unique to each password—prevents rainbow table attacks. Many systems use 100,000 to 600,000 iterations, though this number increases as computing power grows.
bcrypt takes a different approach, incorporating the Blowfish cipher in a purposefully expensive algorithm. Its adaptive nature allows increasing the work factor over time without changing the algorithm. The work factor parameter (typically 10-12) determines computational cost exponentially—each increment doubles the time required. Enterprise identity systems and frameworks like Django and Ruby on Rails default to bcrypt for password storage.
Argon2 represents the state of the art in password hashing, winning the Password Hashing Competition in 2015. Unlike its predecessors, Argon2 defends against both CPU-based and GPU-based attacks by requiring significant memory. The memory-hard property makes parallel attacks on specialized hardware economically infeasible. Three variants exist: Argon2d (maximum resistance to GPU attacks), Argon2i (optimized for password hashing), and Argon2id (hybrid approach recommended for most use cases).
Cryptographic Key Derivation
Beyond passwords, systems often need to derive multiple keys from a single master key. HKDF (HMAC-based Key Derivation Function) standardizes this process, extracting and expanding entropy to produce multiple cryptographic keys from one source. Signal Protocol and many TLS implementations use HKDF to derive encryption keys, authentication keys, and initialization vectors from shared secrets.
The importance of proper key derivation cannot be overstated. Weak KDF implementations have led to numerous breaches. LinkedIn's 2012 breach exposed 6.5 million passwords partly because they used SHA-1 without salts or sufficient iterations—a cautionary tale about inadequate key derivation.
Key Rotation: Managing Cryptographic Lifecycles
Even strong encryption algorithms and properly derived keys eventually require replacement. Key rotation—the practice of periodically replacing cryptographic keys—forms a critical component of defense-in-depth security.
Why Key Rotation Matters
Cryptographic keys face multiple threats over time. Long-lived keys accumulate exposure—every encryption operation leaks minuscule amounts of information about the key. While individual leaks prove insignificant, aggregate exposure over millions of operations can weaken security. Additionally, longer key lifespans increase the window of opportunity for attackers and the potential damage from undetected compromises.
Compliance frameworks mandate key rotation. PCI DSS requires annual encryption key changes for payment card data. HIPAA and GDPR, while not prescribing specific intervals, expect regular key rotation as part of reasonable security measures.
Rotation Strategies and Implementation
Automated rotation represents the ideal approach. Cloud providers like AWS KMS and Azure Key Vault offer built-in rotation with configurable schedules. These systems maintain key versions, automatically re-encrypt data, and handle the complex orchestration required for zero-downtime rotation.
Key versioning allows systems to maintain multiple active keys simultaneously. New data encrypts with the current key version while old data remains encrypted with previous versions. This approach enables gradual migration without service interruptions. A typical implementation stores a key version identifier alongside encrypted data, allowing decryption with the appropriate historical key.
Rotation frequency depends on several factors: data sensitivity, compliance requirements, system capabilities, and operational overhead. High-security environments might rotate daily, while typical enterprise applications rotate monthly or quarterly. The key insight: any rotation proves better than none.
Practical Rotation Patterns
Envelope encryption simplifies rotating large datasets. Rather than re-encrypting terabytes of data, systems encrypt data with data encryption keys (DEKs), then encrypt those DEKs with a key encryption key (KEK). Rotating the KEK only requires re-encrypting the relatively small DEKs—a process completing in seconds rather than hours.
Google Cloud Storage, AWS S3, and Azure Blob Storage all implement envelope encryption, enabling practical key rotation at massive scale. This architectural pattern demonstrates how thoughtful design choices multiply to enable security practices that would otherwise prove infeasible.
Real-World Implementation Considerations
Building secure systems requires balancing multiple concerns. Performance, usability, compliance, and security often pull in different directions.
Performance and Scalability
Encryption inevitably adds computational overhead. However, modern systems minimize this impact through hardware acceleration and intelligent caching. AES-NI reduces AES encryption overhead to negligible levels—often under 1% CPU impact. Key derivation presents higher costs, but these occur infrequently (typically only during authentication) and can be parallelized.
At scale, key management becomes the bottleneck rather than encryption itself. Systems processing millions of requests per second often cache decrypted DEKs in memory, reducing key derivation and decryption overhead. This caching introduces security tradeoffs—cached keys face memory disclosure risks—but proves necessary for performance at scale.
Operational Excellence
Key management failures represent a catastrophic scenario—lost keys mean permanently inaccessible data. Enterprise systems implement robust key backup and recovery procedures. Hardware Security Modules (HSMs) provide tamper-resistant key storage with built-in redundancy. Cloud KMS services replicate keys across multiple regions, ensuring availability even during regional outages.
Regular testing of key recovery procedures prevents disaster. Many organizations conduct quarterly key recovery drills, similar to disaster recovery testing. These exercises verify that documented procedures work correctly and staff understand their roles during an incident.
Advantages and Trade-offs
Strong cryptographic practices deliver compelling benefits while introducing complexity and costs.
Security benefits extend beyond compliance. Defense-in-depth through multiple encryption layers, reduced breach impact through limited key lifespans, and cryptographic agility enabling algorithm migration all strengthen security posture. Systems designed with proper key management adapt as threats evolve.
Operational complexity represents the primary disadvantage. Key rotation requires careful orchestration to avoid data loss. Multiple encryption layers complicate debugging and troubleshooting. Key management infrastructure adds components that themselves require securing and monitoring.
Performance overhead varies significantly. Symmetric encryption adds minimal CPU cost with hardware acceleration. Key derivation intentionally slows authentication but only affects login performance. Asymmetric operations remain expensive, limiting their use to key exchange rather than bulk encryption.
The trade-off centers on proportionality—matching security measures to actual risks. A blog platform likely doesn't need Argon2 with maximum settings and daily key rotation, while a banking application absolutely does.
Architectural Patterns for Key Management
Large-scale systems converge on several proven architectural patterns.
Centralized key management services (AWS KMS, Google Cloud KMS, Azure Key Vault) provide significant advantages: consistent security policies, centralized audit logs, simplified compliance reporting, and expert-managed infrastructure. These services eliminate much of the operational burden while providing strong security guarantees.
Service-per-tenant keys isolate blast radius in multi-tenant systems. Rather than one master key protecting all customer data, each tenant receives dedicated keys. Compromising one tenant's keys doesn't affect others—a crucial property for SaaS platforms.
Separation of duties ensures no single person or system controls all key management aspects. Creating keys, rotating keys, and accessing encrypted data typically require different permissions. This separation prevents insider threats and limits damage from compromised credentials.
Conclusion
Effective cryptographic key management combines algorithm selection, proper key derivation, and disciplined rotation practices. Modern systems benefit from decades of cryptographic research and battle-tested implementations.
Start with established algorithms—AES for symmetric encryption, RSA or ECC for asymmetric operations. Use Argon2 or bcrypt for password-based key derivation, never implementing custom solutions. Implement automated key rotation from day one, even if initially set to generous intervals.
Leverage managed services when possible. Cloud provider key management solutions offer enterprise-grade security with minimal operational overhead. This allows teams to focus on application security rather than cryptographic infrastructure.
Security evolves continuously. Algorithms once considered secure become vulnerable as computational power increases and new attacks emerge. Building systems with cryptographic agility—the ability to swap algorithms without major rewrites—ensures long-term security resilience.
The technical community benefits when organizations share lessons learned and architectural patterns. As threats grow more sophisticated, collective knowledge and proven practices become increasingly valuable.