RSA JWT Encryption and Key Rotation in Enterprise GitOps: A Practical Guide
JSON Web Tokens (JWTs) have become the de facto standard for authentication and authorization in modern distributed systems. When combined with RSA encryption and proper key rotation strategies, they provide a robust security foundation for enterprise applications. However, managing cryptographic keys in GitOps environments presents unique challenges that require careful architectural consideration.
Understanding RSA JWT Encryption
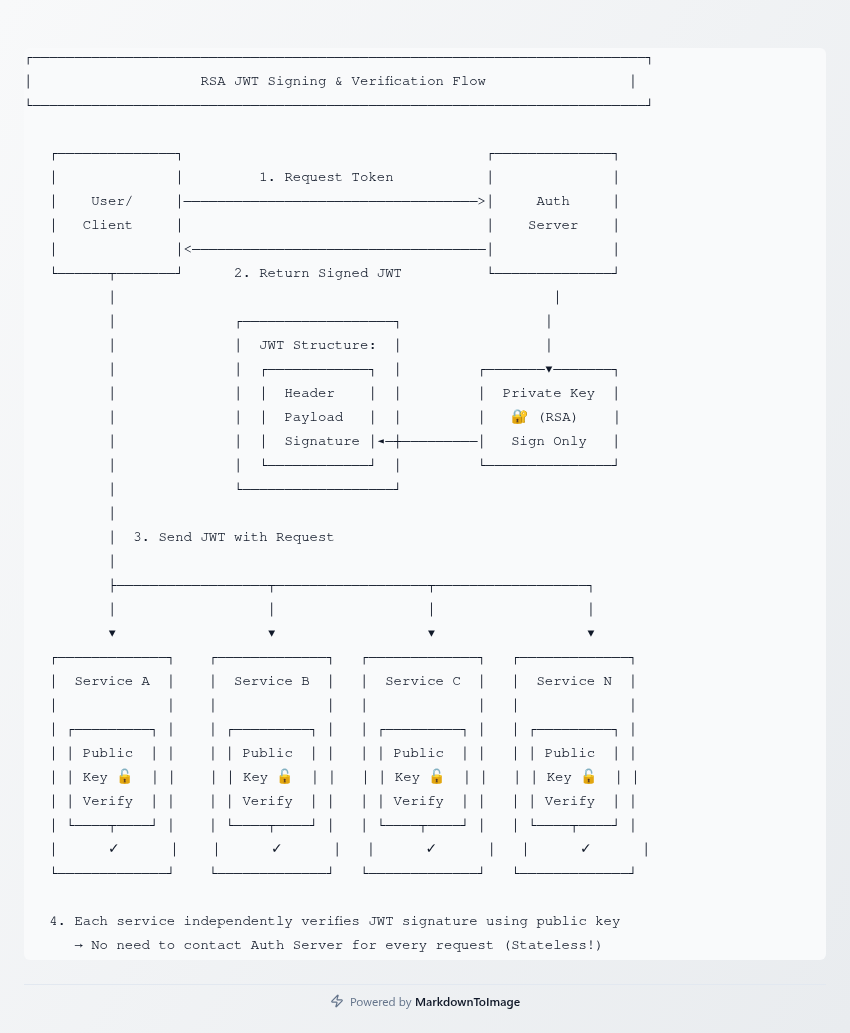
RSA (Rivest-Shamir-Adleman) is an asymmetric encryption algorithm that uses a pair of keys: a private key for signing and a public key for verification. In JWT implementations, the authorization server signs tokens with a private key, while resource servers verify signatures using the corresponding public key. This asymmetric approach eliminates the need to share secret keys across services, significantly reducing the attack surface.
The signing process involves creating a JWT with header, payload, and signature components. The header specifies the algorithm (typically RS256, RS384, or RS512), the payload contains claims about the user and token metadata, and the signature ensures integrity. When a client presents a JWT, services can verify its authenticity using the public key without contacting the authorization server, enabling stateless authentication at scale.
RSA offers several advantages over symmetric algorithms like HMAC-SHA256. Public keys can be distributed freely, making verification straightforward in microservices architectures. The private key remains secured in a single location, typically the authorization server. This separation of concerns allows different teams to manage authentication and resource services independently.
The Critical Need for Key Rotation
Key rotation is not optional—it's a fundamental security requirement. Cryptographic keys have a limited lifespan due to several factors: the risk of compromise increases over time, computational advances make older keys vulnerable, and compliance frameworks mandate regular rotation. Industry standards typically recommend rotating signing keys every 90 to 180 days, though some high-security environments rotate monthly or even weekly.
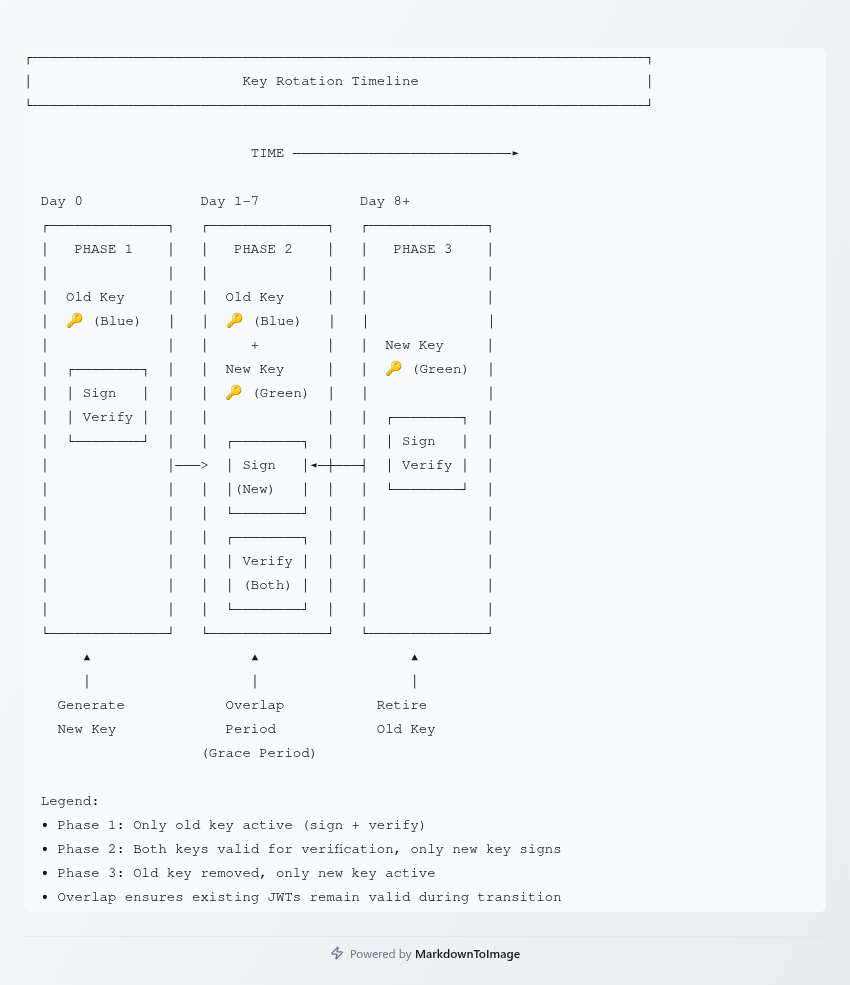
The rotation process must be seamless to avoid service disruptions. The standard approach uses overlapping key validity periods. Before decommissioning an old key, the new key must be distributed to all services. During the transition period, both keys remain valid for verification, but only the new key is used for signing. This overlap ensures that tokens signed with the old key continue to work while new tokens use the updated key.
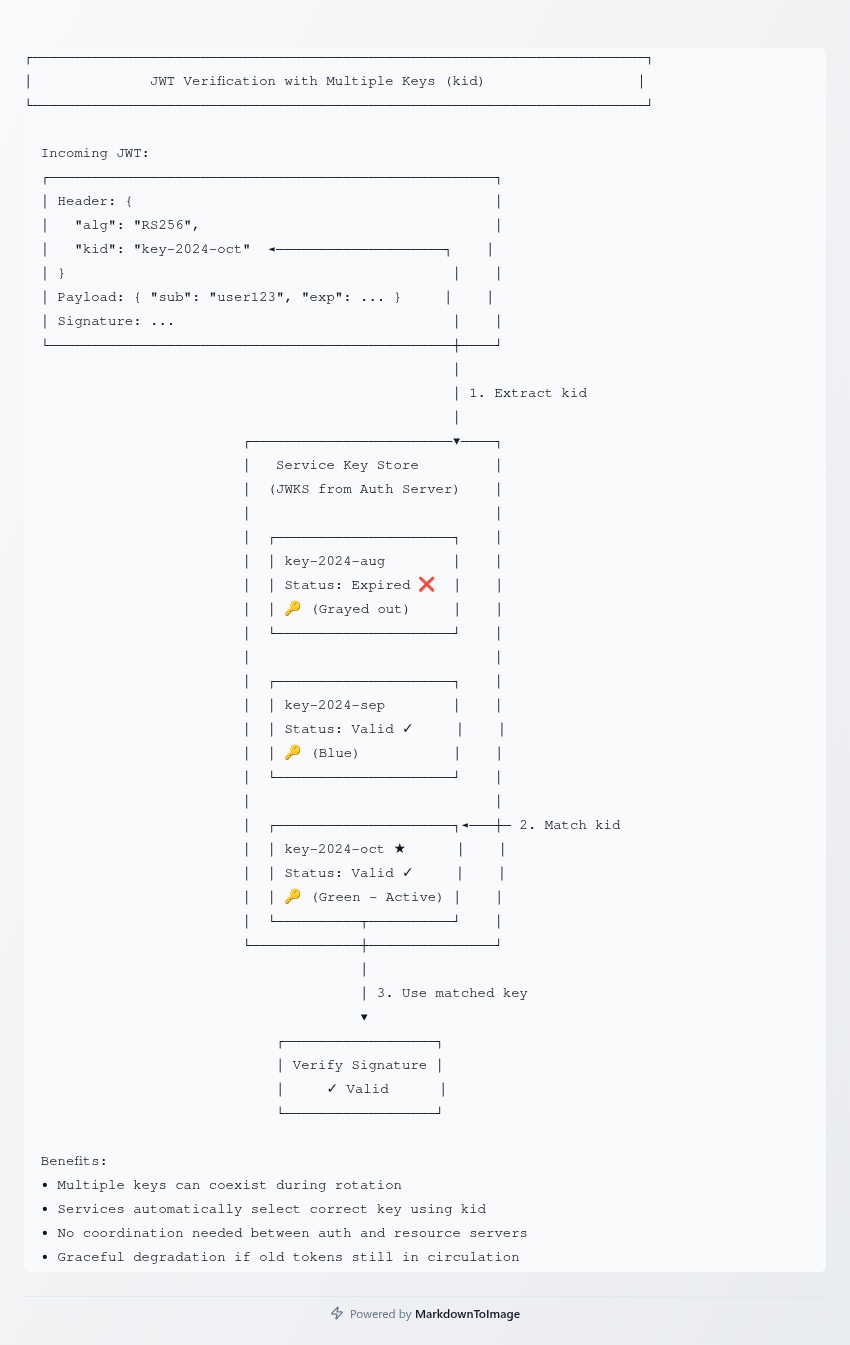
Key identifiers (kid) in the JWT header play a crucial role in rotation. Each key pair receives a unique identifier, and services use this kid to select the appropriate public key from their keystore. When multiple keys are valid simultaneously, the kid disambiguates which key signed a particular token. This mechanism enables graceful rotation without requiring simultaneous updates across all services.
Enterprise GitOps Key Storage Architecture
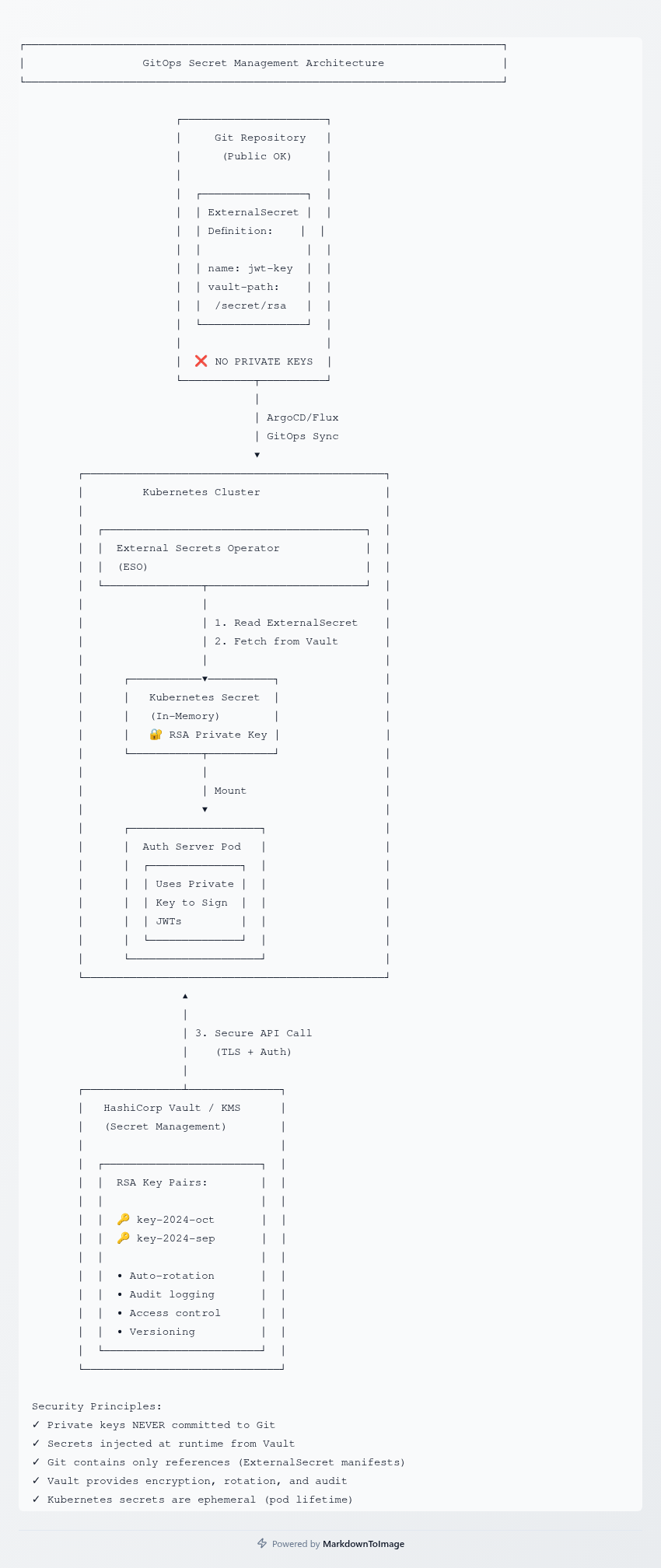
Storing cryptographic keys in GitOps environments requires balancing security, automation, and operational efficiency. The fundamental principle is clear: never commit raw private keys to Git repositories. Even private repositories can be compromised, and version control systems retain historical data indefinitely. A single accidental commit could expose keys permanently.
The enterprise approach uses sealed secrets or external secret management systems. Tools like Sealed Secrets, External Secrets Operator, or SOPS (Secrets OPerationS) encrypt sensitive data before it enters Git. Sealed Secrets, for example, uses asymmetric encryption where only the in-cluster controller can decrypt secrets. The encrypted data safely resides in Git alongside application configurations, while the decryption key remains secured within the Kubernetes cluster.
For production environments, dedicated secret management platforms provide enhanced security. HashiCorp Vault, AWS Secrets Manager, Azure Key Vault, and Google Cloud Secret Manager offer features beyond basic encryption: automatic rotation, fine-grained access control, audit logging, and versioning. These systems integrate with GitOps workflows through operators that sync secrets into clusters without exposing them in Git repositories.
The typical architecture separates secret definitions from secret values. Git repositories contain references or pointers to secrets, not the secrets themselves. For example, an ExternalSecret resource specifies which secret to retrieve from Vault and where to place it in Kubernetes, but the actual RSA private key remains in Vault. This pattern maintains GitOps benefits—declarative configuration, version control, and automated deployment—while ensuring cryptographic material never touches Git.
Implementing Automated Key Rotation
Automated rotation requires coordination between multiple components. The secret management system generates new key pairs on schedule, the authorization server begins using new keys for signing, public keys propagate to verification services, and old keys eventually retire after their tokens expire. This choreography must be reliable, auditable, and reversible in case of issues.
A practical implementation might use HashiCorp Vault's Transit secrets engine to generate and rotate RSA keys automatically. The authorization server retrieves the current signing key from Vault's API without persistent storage. Services download public keys from a JWKS (JSON Web Key Set) endpoint that the authorization server exposes. This endpoint returns all currently valid public keys with their kid identifiers, allowing services to cache keys and refresh periodically.
The rotation workflow typically follows this sequence: Vault generates a new RSA key pair with a unique kid, the authorization server detects the new key through Vault's API, the JWKS endpoint begins advertising both old and new public keys, the authorization server switches to signing with the new key, verification services refresh their key cache and can now verify tokens signed with either key, and after the maximum token lifetime elapses (commonly 1 hour for access tokens), the old key is removed from JWKS and marked for deletion in Vault.
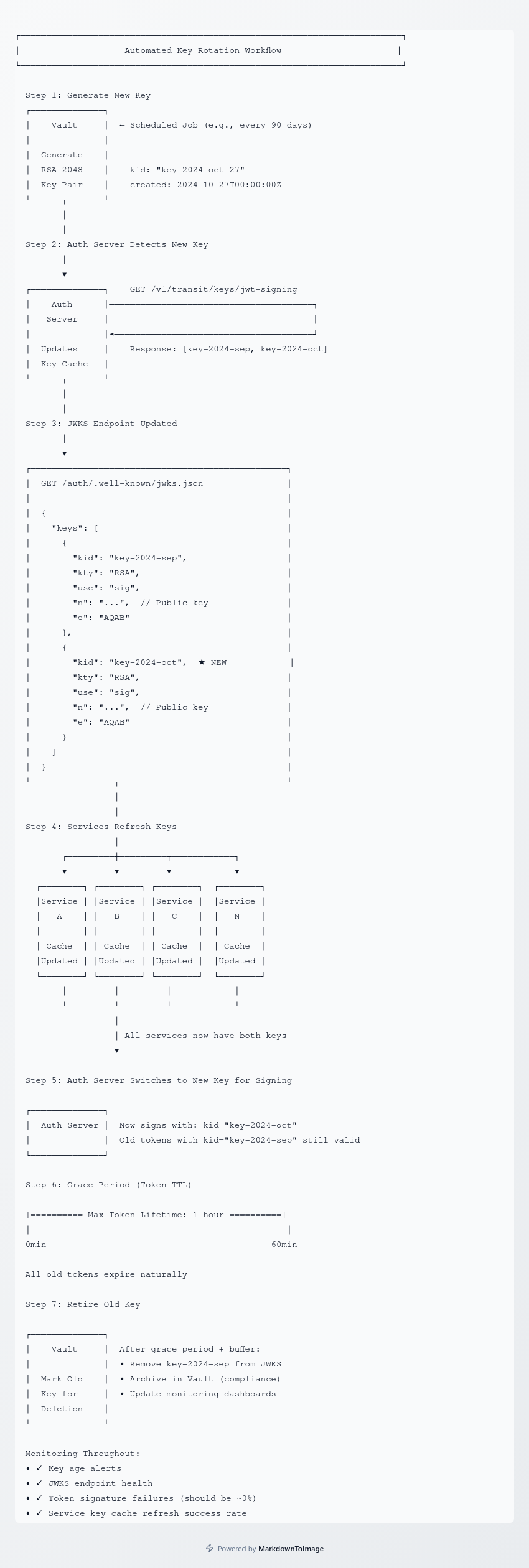
Monitoring and alerting are essential. Track key age to ensure rotation occurs on schedule, monitor JWKS endpoint availability to prevent verification failures, log all signing operations with kid identifiers for audit trails, and alert when key propagation takes longer than expected. Failed rotations can lock users out entirely, so robust testing and rollback procedures are non-negotiable.
Real-World Implementation Patterns
Large enterprises often adopt a multi-tier key hierarchy. A root key stored in a Hardware Security Module (HSM) or cloud KMS rarely changes and encrypts intermediate keys. Intermediate keys, rotated quarterly, encrypt the actual JWT signing keys. The signing keys rotate frequently (daily to weekly) but can be recovered from intermediate keys if needed. This hierarchy balances security and operational flexibility.
In multi-region deployments, key distribution becomes complex. A centralized Vault cluster with replication can serve multiple regions, but network partitions could prevent key access. Some architectures use regional Vault clusters that synchronize keys asynchronously. Others pre-distribute keys to regions before activation, accepting brief windows where different regions use different signing keys. Services must download JWKS from multiple regions to handle this eventually-consistent scenario.
Zero-downtime rotation requires careful orchestration. Blue-green deployment strategies can help: deploy the new authorization server version with updated keys alongside the old version, gradually shift traffic to the new version while monitoring error rates, allow sufficient time for old tokens to expire, and finally decommission the old version. Feature flags can control which key the authorization server uses for signing, enabling instant rollback if problems emerge.
Security Considerations and Trade-offs
Key size impacts both security and performance. RSA-2048 is the minimum acceptable standard today, offering adequate security for most applications. RSA-4096 provides greater security margin but increases signature generation and verification time by roughly 4x. High-throughput systems may struggle with RSA-4096, making the 2048-bit option more practical unless regulatory requirements demand otherwise.
Access control for private keys must be draconian. In Vault, policies should restrict key access to the authorization server's service account only. Even administrators shouldn't retrieve private keys directly—Vault's sign operations allow the authorization server to request signatures without extracting the key. This pattern ensures keys never leave the secret management system, minimizing exposure risk.
Backup and disaster recovery planning must account for key material. If Vault or the secret management system becomes unavailable, services can continue verifying existing tokens using cached public keys, but no new tokens can be issued. Document the recovery time objective (RTO) and recovery point objective (RPO) for your secret management infrastructure. For critical systems, consider running Vault in high-availability mode across multiple availability zones with automated failover.
Advantages and Disadvantages
The RSA JWT approach offers significant benefits. Stateless verification scales horizontally without shared state, public key distribution is safe and straightforward, and different services can use different key pairs for isolation. Services don't need network connectivity to the authorization server for every verification, reducing latency and improving resilience.
However, RSA signatures are computationally expensive compared to symmetric algorithms. High-throughput systems may need to optimize verification with key caching, connection pooling, and horizontal scaling. Key management infrastructure adds operational complexity—Vault, sealed secrets operators, and rotation automation require dedicated expertise. Small teams might find this overhead prohibitive initially.
The GitOps integration challenge is real. Automated secret management can conflict with GitOps principles of "Git as the source of truth." When secrets live outside Git, the actual deployed state isn't fully represented in the repository. This trade-off is necessary for security, but it requires adapted operational practices and additional tooling for complete system visibility.
Architectural Best Practices
Start with a phased approach. Implement basic JWT verification with RSA first, ensuring services can validate signatures correctly. Add JWKS support so services automatically discover public keys without manual configuration. Introduce automated rotation with generous overlap periods, reducing the window only after proving stability. Finally, integrate with enterprise secret management and GitOps workflows.
Design for failure modes. What happens if Vault is unreachable during rotation? What if the JWKS endpoint returns stale data? Services should cache public keys with reasonable TTLs (5-15 minutes), gracefully handle rotation by attempting verification with multiple keys, log verification failures with sufficient detail for debugging, and implement circuit breakers to prevent cascade failures when the authorization server is struggling.
Document the key lifecycle explicitly. Maintain a runbook covering normal rotation procedures, emergency key revocation, disaster recovery, and compliance auditing. Include specific commands, API calls, and verification steps. This documentation proves invaluable during incidents when quick action is required.
Moving Forward
RSA JWT encryption with automated key rotation provides a solid foundation for enterprise authentication. The complexity is justified by the security benefits, especially as organizations scale to hundreds of services and thousands of developers. GitOps integration, while challenging, enables the infrastructure-as-code practices that modern teams expect.
The key to success lies in incremental implementation. Start small, validate each component thoroughly, and expand gradually. Invest in monitoring and alerting early—visibility into key rotation health prevents surprises. And remember that security is a continuous process, not a destination. Regular audits, penetration testing, and staying current with cryptographic best practices ensure your JWT infrastructure remains robust against evolving threats.