The Software Architect’s Guide to Zero-Trust in 2026: Beyond the VPN
The classic "castle-and-moat" security model—where we fiercely guard the perimeter but trust everyone inside—is fundamentally broken in the era of hybrid work, cloud saturation, and decentralized assets. Today's network isn't defined by physical walls; it's defined by identity and context. We need to stop thinking about a single, static perimeter and start building thousands of dynamic perimeters around every user, every device, and every data flow. This is the essence of Zero-Trust Architecture.
As architects, we have a unique responsibility: we cannot simply bolt security onto an existing system. Zero-Trust is a fundamental design philosophy that must be woven into the fabric of our applications, infrastructure, and workflows from day one. It demands that we challenge every assumption about trust and verify everything, constantly.
1. Core Principles: The 3 Pillars of Zero-Trust
Before we dive into technical implementation, let’s ground ourselves in the foundational principles that define a Zero-Trust approach. This isn't just about software; it’s a mindset shift that recalculates risk.
Principle 1: Verify Explicitly
The era of implicit trust is over. "Verify Explicitly" means that we must authenticate and authorize every request, regardless of where it originates. Just because a request comes from inside the corporate network doesn't make it safe.
From an architectural standpoint: This means identity is the first class concern. We must design systems that can ingested verified context (user identity, device health, location, time) and use that context to make access decisions.
Principle 2: Apply Least-Privilege Access
We’ve all seen it: a user has full admin rights to a production database because they might need to troubleshoot "one time." Zero-Trust mandates that we limit access to the exact minimum required to perform a task. This concept, known as Just-In-Time (JIT) and Just-Enough-Access (JEA), is crucial.
From an architectural standpoint: We move beyond static, binary access control (e.g., "admin vs. user"). We design granular, dynamic policies that allow us to grant specific permissions for limited durations, reducing the blast radius of any compromised account.
Principle 3: Assume Breach
This is the most critical cultural shift. You must operate under the assumption that an attacker is already inside your system or soon will be. This principle forces us to stop focusing solely on detection and start focusing on containment.
From an architectural standpoint: We must implement deep micro-segmentation. We design our network so that a compromised service cannot automatically lateral-move to another. Every transaction, even service-to-service calls within the same data center, must be scrutinized.
2. Architecting the ZTA Control Plane
The control plane is the nervous system of your ZTA. It’s responsible for evaluating access requests and issuing the policies that data planes (your actual networks and applications) enforce.
A robust ZTA control plane typically includes:
A. Dynamic Policy Engine
This is the central brain. It receives signals (the context) from various sources and evaluates them against predefined access policies to make a realtime decision. This engine must be highly available and resilient.
B. Identity & Context Sources (SIGNAL)
This is the data feed that powers the Policy Engine. It’s not just your identity provider (like Azure AD or Okta); it includes:
- User Context: MFA status, user behavior anomalies (UEBA).
- Device Context: Is the OS patched? Is endpoint security active? (MDM integration).
- Network Context: Is the source IP expected? Is the request coming via a known path?
- Data Context: What sensitivity level is the data being accessed?
C. Policy Enforcement Points (PEP)
These are the gateways where access decisions are enforced. In modern architecture, PEPs are implemented at various layers:
- Network Proxies / SASE: Controlling network-level access.
- Service Mesh Sidecars: Controlling service-to-service communication.
- API Gateways: Authorizing API requests based on OAuth scopes.
D. Centralized Logs & Visibility
Zero-Trust generates massive amounts of telemetry. The control plane must feed this data into a SIEM (Security Information and Event Management) system to detect anomalies and refine access policies continuously. Continuous validation is an iterative feedback loop.
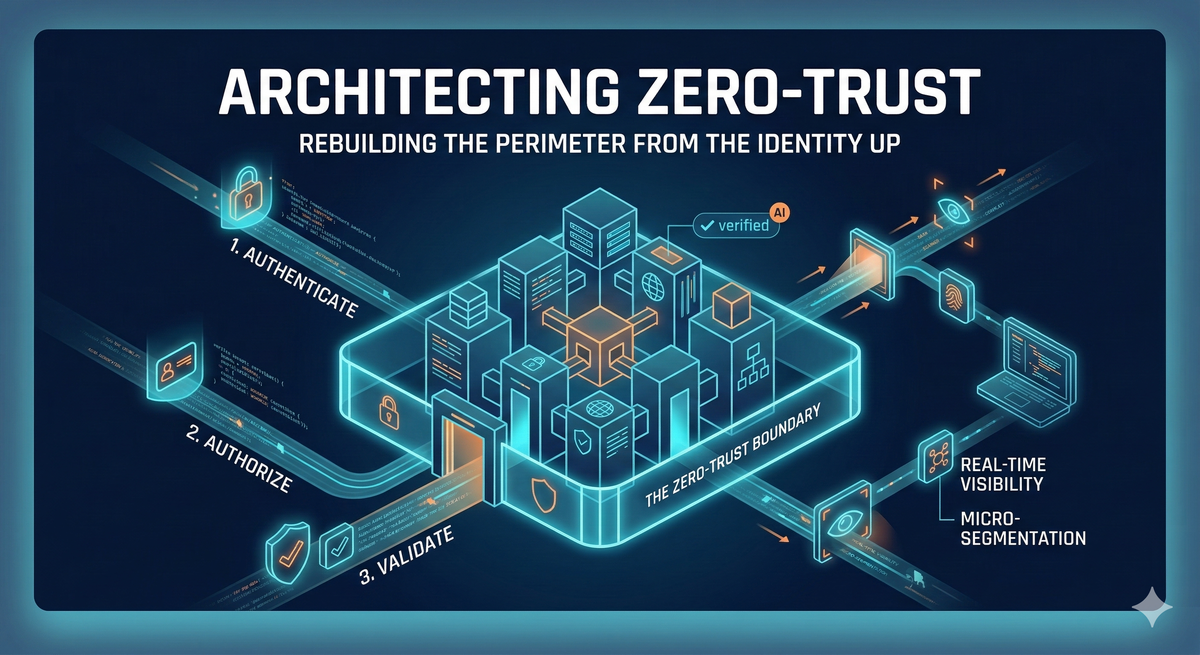
3. Implementing the Zero-Trust Boundary
Let's look at the concrete patterns for building that boundary shown in the illustration. You don't have to boil the ocean on day one. A successful ZTA rollout is a phased, capability-based maturity journey.
Layer 1: The Network Boundary (Micro-segmentation)
Instead of one large network segment, we create tiny, defined zones for related applications or data. The goal is simple: if a single app server is compromised, the attacker cannot easily pivot to the financial database next to it.
Architectural Focus: Leverage software-defined networking (SDN) and service mesh technologies to isolate workloads at a granular level. The internal "Verified checkmark" in the illustration is a visualization of this internal, validated state.
Layer 2: The Application Boundary (Identity-Aware Proxy)
Move away from legacy VPNs. An Identity-Aware Proxy (IAP) acts as the single entry point for all application access. Before the first byte of application data is sent, the IAP validates the user’s identity and the health of their device.
Architectural Focus: Intercept traffic and validate identities at the application layer before sending the request to the backend.
Layer 3: The Data Boundary (Scoped Access)
The data itself must be protected by fine-grained access policies. This goes beyond network isolation and means evaluating requests at the database or object storage level.
Architectural Focus: Move to a world where data access is defined by explicit entitlements, often using attribute-based access control (ABAC). We no longer rely on a service having a "super-user" service account.
Conclusion: The Architect's Mandate
Zero-Trust Architecture isn't a silver bullet, and it’s not something you can just buy. It’s a design philosophy that must be embraced at the highest architectural levels. Our mandate as senior engineers and architects is to recognize that identity is the new perimeter.
By embracing "Verify Explicitly," "Least-Privilege," and "Assume Breach," and by leveraging the powerful new tooling that supports a ZTA control plane, we can build inherently more secure systems that protect our assets, no matter where they reside. Rebuilding the perimeter from the identity up is the only path forward.